Mastering Cybersecurity – Safeguard Your Data Against Digital Threats: In the high-tech age we live in, cybersecurity has become more than just a buzzword; it is a crucial practice everyone must learn and implement.
We live in an era of ever-evolving digital threats, where cybercriminals are continuously inventing new ways to infiltrate systems, steal data, and disrupt lives.
Inspiring your journey, one story at a time. #LifeFalcon.
This article delves into the core aspects of cybersecurity, providing comprehensive information on how you can safeguard your data and protect yourself from cyber attacks.
Table of Content
Understand the Threat Landscape
It’s crucial to comprehend the current digital threat landscape to safeguard your data effectively. The digital world is teeming with different kinds of threats, from relatively simple phishing scams to complex ransomware attacks. Three aspects are essential when understanding these threats: their variety, the methods used, and the potential damage they can cause.
A diverse array of cyber threats exists, and they’re constantly evolving. For instance, phishing scams may trick you into revealing your login credentials, while ransomware locks up your computer or encrypts your files until you pay a ransom. Other threats include malware, spyware, and Denial-of-Service (DoS) attacks, each designed to cause specific harm.
Each threat type deploys unique tactics to infiltrate systems and networks. For example, a phishing scam might involve a seemingly genuine email from a trusted source, while ransomware might exploit security vulnerabilities in software applications. Understanding these tactics can help you recognize and avoid such threats.
The potential damage from cyber threats varies, too. A successful phishing attack could lead to identity theft, a ransomware attack could result in loss of data or financial loss, and a DoS attack could disrupt services for extended periods. Being aware of these consequences underscores the importance of proactive cybersecurity measures.
Implement Robust Password Practices
One of the simplest yet most effective measures you can take to protect your data is implementing strong password practices. This aspect is often overlooked, leading to data breaches. Three key facets should be remembered when considering password practices: complexity, uniqueness, and regular changes.
Your passwords should be complex, using a mix of uppercase and lowercase letters, numbers, and special characters. This complexity makes it difficult for cybercriminals to guess your password or crack it using brute force methods.
Uniqueness is equally important. Using the same password for multiple accounts can lead to a domino effect if one account is compromised. Therefore, make sure to use a unique password for every account.
Lastly, make it a habit to change your passwords regularly. Even if a cybercriminal manages to get hold of your password, frequent changes will limit the damage they can cause.
Use Two-Factor Authentication
Two-factor authentication (2FA) is another effective measure to enhance your cybersecurity. It adds an extra layer of protection to your accounts by requiring a second form of identification beyond just your password. This could be a text message sent to your phone, a biometric identifier like a fingerprint, or a unique code generated by an app.
Implementing 2FA significantly increases your account’s security. Even if a cybercriminal manages to get hold of your password, they would need the second identifier to access the account. This makes it much more difficult for unauthorized access to occur, protecting your data from potential breaches.
Regularly Update Software
Regular software updates are another essential aspect of effective cybersecurity. These updates often include patches for known security vulnerabilities that cybercriminals could otherwise exploit. Three key considerations are the importance of regular updates, the risks of not updating, and the benefits of automatic updates.
Regularly updating your software is vital to ensuring the security of your data. Updates often include patches that fix known security vulnerabilities. By not updating, you are leaving your systems open to exploitation.
Not updating your software can expose you to a variety of risks. Cybercriminals often exploit known vulnerabilities in outdated software, which can lead to data breaches and other security incidents. Therefore, it’s crucial to keep your software up to date.
Consider enabling automatic updates where possible. This ensures that your software remains up-to-date without you having to manually check for updates. It’s a simple step, but it can significantly improve your overall cybersecurity.
Employ a Reliable Antivirus Solution
Employing a reliable antivirus solution is a fundamental cornerstone in building a formidable cybersecurity defense. The key roles of this software include identifying, quarantining, and eliminating malware threats before they can do significant damage. They serve as a watchdog, consistently monitoring your system for any anomalies that hint at the presence of malicious software.
Remember, the digital world is fraught with a variety of malware forms: viruses, trojans, ransomware, spyware, adware, and more. Each poses unique threats to your data and systems. Herein lies the value of a comprehensive antivirus solution. They are designed to tackle this multitude of threats, using advanced algorithms to detect and neutralize them.
Beyond detection and removal, modern antivirus solutions also provide real-time protection. They are designed to operate in the background, checking files as you access them to ensure no hidden threats lie within. This active protection can stop a malware infection in its tracks, preventing it from spreading or causing damage.
Moreover, top-tier antivirus solutions offer features like phishing protection, blocking malicious websites that aim to trick you into giving away personal information. Some even include additional protective layers such as firewalls and spam filters.
Another important aspect to consider is the frequency of updates for your chosen antivirus software. New malware variants emerge daily, and an outdated antivirus might not recognize these novel threats. Therefore, it’s crucial to choose an antivirus solution that provides frequent updates, ensuring it’s equipped to identify and combat the latest malware types.
Adopt Safe Browsing Habits
Adopting safe browsing habits is a fundamental step in securing your data. This is particularly important when engaging in online activities such as playing online casino games where personal and financial information is often shared.
Understanding the implications of your online behavior involves recognizing that every website you visit, every link you click, and every file you download can potentially expose you to cyber threats. Cybercriminals often exploit unsafe browsing habits to inject malware, initiate phishing scams, and carry out other malicious activities.
Using the right tools can greatly enhance your online safety. This can include web browser security settings, add-ons that block ads and trackers, and virtual private networks (VPNs) that encrypt your internet connection and hide your online activities.
Practicing discernment involves being careful with what you download, avoiding clicking on suspicious links, and not providing personal or sensitive information unless you’re certain the website is secure and legitimate.
Back Up Your Data Regularly
Regular data backups are an important part of cybersecurity. If a cyber-attack compromises your data, having a recent backup can help you recover quickly. Consider the three-pronged approach: the significance of backups, the 3-2-1 rule, and the different backup methods available.
The importance of backups cannot be overstated. They serve as a safety net, ensuring that even if your data is compromised, you can restore it and mitigate the impact of the attack.
The 3-2-1 backup rule is a simple guideline to follow. It suggests having at least three copies of your data, stored on two different types of media, with one stored offsite or in the cloud.
There are multiple methods to back up data, such as local backups on an external hard drive or using cloud-based backup services. The method you choose should depend on your specific needs and circumstances.
Be Aware of Social Engineering Attacks
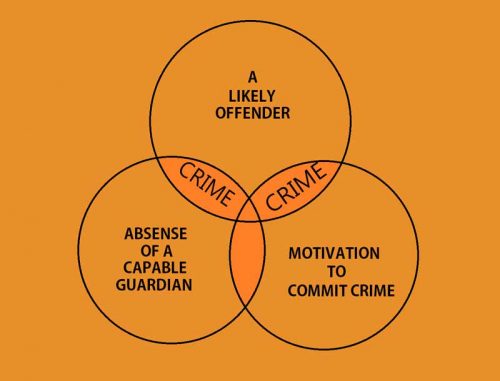
Social engineering is a sophisticated technique used by cybercriminals that manipulates people into divulging confidential information. To protect yourself, it’s crucial to understand what social engineering is, recognize its common forms, and learn how to respond.
Social engineering can take many forms, but its essence is deception. Whether it’s a phone call from someone pretending to be your bank or an email from a seemingly trusted source, these attacks aim to trick you into revealing sensitive information.
Common forms of social engineering attacks include phishing emails, baiting with free downloads, and pretexting where attackers create a fabricated scenario to gain your trust. Understanding these tactics will help you identify and avoid potential threats.
If you believe you’re being targeted by a social engineering attack, it’s important not to respond or provide any information. Instead, contact the relevant organization directly using a known and trusted method.
Educate Yourself and Stay Informed
Lastly, educating yourself and staying informed about the latest cybersecurity threats and protection measures is critical. The world of cybersecurity is constantly evolving, and being knowledgeable about these changes can significantly enhance your defense against cyber attacks.
A great way to stay informed is by following reliable cybersecurity news sources and blogs, participating in webinars, or even enrolling in online courses. This will ensure that you’re up-to-date with the latest information and best practices in the field.
In summary, adopting safe browsing habits, regularly backing up your data, being aware of social engineering attacks, and educating yourself about cybersecurity are four additional strategies to safeguard your data against digital threats. By implementing these measures, you’ll be better equipped to protect your digital environment and reduce the risk of falling victim to cyber-attacks. Cybersecurity isn’t just a technical challenge, but a personal responsibility that we all should embrace.